Difference Between Anomaly Detection And Misuse Detection
Between backward and forward stepwise selection theres just one fundamental difference which is whether youre. AC-6 CM-2 RA-5 SA-5 SC-7.
Soft Computing For Anomaly Detection And Prediction To Mitigate Iot Based Real Time Abuse Springerlink
Breaches by the Numbers There are many factors to consider when preparing for and managing a data breach such as the amount of time it takes to respond to a data breach and the reputational impact it has on your company.

Difference between anomaly detection and misuse detection. Blood doping is a form of doping in which the number of red blood cells in the bloodstream is boosted in order to enhance athletic performance. Intrusion detection system ppt 1. Organizations can utilize network scanning tools intrusion detection and prevention systems and end-point protections such as firewalls and host-based intrusion detection systems to identify and prevent the use of prohibited functions ports protocols and services.
HIDSs running signature-based detection work somewhat similarly to antivirus applicationswhich search for bit patterns or. ChangAfter that Daniel spent two years at the Georgia Institute of Technology as a post-doctoral research. Ability to provide timely detection identification and alerts of possible attacksintrusions anomalous activities and misuse activities and distinguish these incidents and events from benign activities Ability to use computer network defense CND tools for continual monitoring and analysis of system activity to identify malicious activity.
In Communication Engineering and MS. Intruders may be from outside theIntruders may be from outside the network or. Stepwise methods have the same ideas as best subset selection but they look at a more restrictive set of models.
Daniel received his BS. Attempting to break into or misuse your systemmisuse your system. Payment disputes are an inevitable consequence of a digital economy.
The largest difference for breaches with a high level of compliance failures compared to a low level was 230 million IBM. In statistics stepwise regression includes regression models in which the choice of predictive variables is carried out by an automatic procedure. The signature-based form of detection monitors data for patterns.
No comparative studies reported nonserious adverse events related to the immune urogenital or other body systems. Attempting to break into orIntrusion. The Complete Chargeback Guide for Merchants and Consumers.
Intrusion and IntrusionIntrusion and Intrusion DetectionDetection Intrusion. A HIDS using anomaly-based detection surveys log files for indications of unexpected behavior while a NIDS monitors for the anomalies in real time. Understand the principles of routing the difference between interior and exterior gateway protocols name some examples of both and explain in very basic terms their principles of operation.
2 Road obstacle detection in range data. Blood doping can be achieved by making the body. We would like to show you a description here but the site wont allow us.
One study with 275 participants DubnovRaz 2011 found no difference between those in the methylphenidate group and those in the no intervention group for BMI z score MD 001 95 CI 022 to 024. As in-person manual transactions are replaced by frictionless card-not-present payments the need to fairly arbitrate disputes between merchants and consumers is more important than ever. Degree in Computer Science from the Hong Kong Polytechnic University under the supervision of Prof.
In Communications and Information Systems from Wuhan UniversityHe obtained his PhD. Explain the basic concepts of IPv6. Because such blood cells carry oxygen from the lungs to the muscles a higher concentration in the blood can improve an athletes aerobic capacity VO 2 max and endurance.
Intrusion DetectionIntrusion Detection SystemSystem 2. We have developed computationally simple algorithms for road obstacle detection and applied them to a variety of synthetic and real range imagery. In contrast to standard classification tasks anomaly detection is often applied on unlabeled data taking only the internal structure of the dataset into account.
This challenge is known as unsupervised anomaly detection and is addressed in. Anomaly detection is the process of identifying unexpected items or events in datasets which differ from the norm.

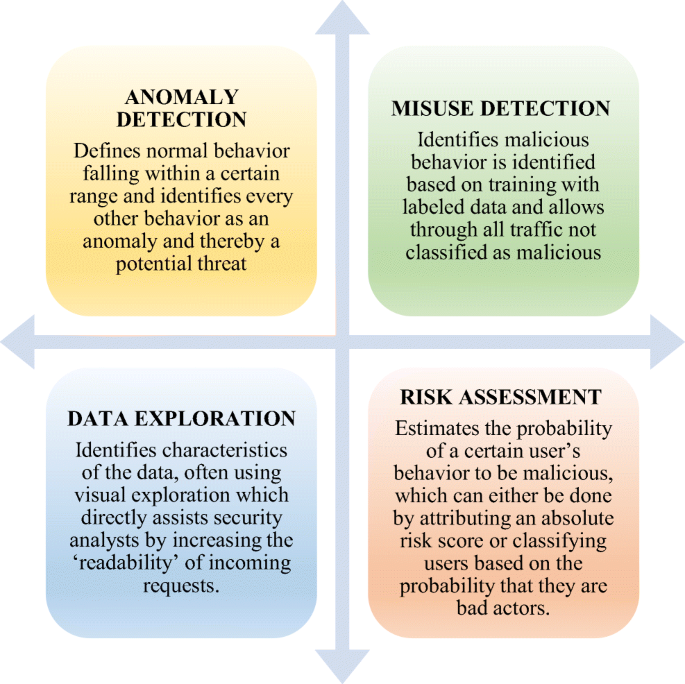
A Comparison Between Misuse And Anomaly Detection Techniques Download Scientific Diagram

A Comparison Between Misuse And Anomaly Detection Techniques Download Scientific Diagram
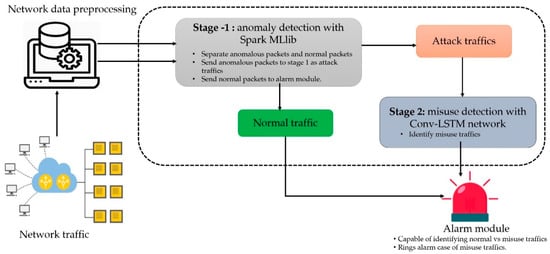
Symmetry Free Full Text A Scalable And Hybrid Intrusion Detection System Based On The Convolutional Lstm Network Html

The Flow Chart Of Misuse Detection And Anomaly Detection Application 10 Download Scientific Diagram
Fusion Of Misuse Detection With Anomaly Detection Technique For Novel Hybrid Network Intrusion Detection System Springerlink

Misuse Based Intrusion Detection Versus Statistical Analysis Based Download Table

Three Categories Of Hybrid Detection Systems A Anomaly Misuse Download Scientific Diagram

A Comparison Between Misuse And Anomaly Detection Techniques Download Scientific Diagram

Ensemble Ids Model The Misuse Or Anomaly Detection Raw Data Has Been Download Scientific Diagram
0 Response to "Difference Between Anomaly Detection And Misuse Detection"
Post a Comment